ニュース
「Microsoft Edge 148」が公開 ~新しいAI設定ページを導入、致命的な脆弱性も修正
2026年5月8日 14:03
米Microsoftは5月7日(現地時間)、デスクトップ向け「Microsoft Edge」v148.0.3967.54を安定(Stable)チャネルでリリースした。「Edge 148」における主な変更は、以下の通り。
- パスワードの自動入力候補がトップレベルドメインの一致で提案されるように:「account.microsoft.com」や「office.microsoft.com」などのWebサイトで同じ認証情報が候補として表示される
- 「Copilot」のある新しいタブページ(NTP):検索ボックスから「Copilot」とのチャットも行える
- Shadow AI:管理者が把握していない生成AIへ機密データが送出されないようにブロックする
- オートフィルの機能強化:保存済みの住所に加え、パスポート、運転免許証など、さまざまな種類のデータを自動入力できるように
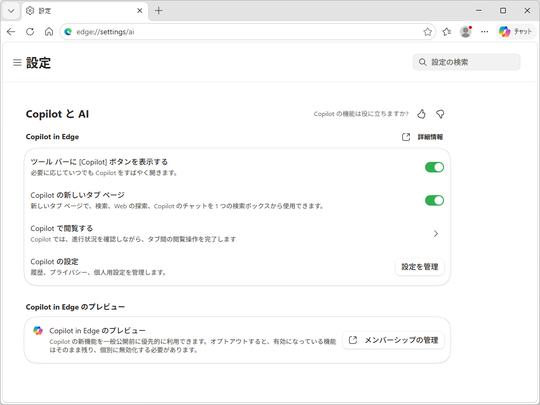
- アップデートされたAI設定ページ(edge://settings/ai):「Copilot」に関する設定をひとまとめに。「Copilot モード」もここから無効化できる
なお、これらの変更の一部は「Controlled Feature Rollout」(CFR)と呼ばれる仕組みで制御されており、段階的にロールアウトされる。そのため、「Edge 148」へアップデートしてもすぐに利用できるようになるとは限らない点には注意したい。
セキュリティ修正
脆弱性の修正は、全121件。うち118件は「Chromium」由来のものだ。
- CVE-2026-7896:Integer overflow in Blink(Critical)
- CVE-2026-7898:Use after free in Chromoting(Critical)
- CVE-2026-7899:Out of bounds read and write in V8(High)
- CVE-2026-7900:Heap buffer overflow in ANGLE(High)
- CVE-2026-7901:Use after free in ANGLE(High)
- CVE-2026-7902:Out of bounds memory access in V8(High)
- CVE-2026-7903:Integer overflow in ANGLE(High)
- CVE-2026-7904:Out of bounds read in Fonts(High)
- CVE-2026-7906:Use after free in SVG(High)
- CVE-2026-7907:Use after free in DOM(High)
- CVE-2026-7908:Use after free in Fullscreen(High)
- CVE-2026-7909:Inappropriate implementation in ServiceWorker(High)
- CVE-2026-7910:Use after free in Views(High)
- CVE-2026-7911:Use after free in Aura(High)
- CVE-2026-7914:Type Confusion in Accessibility(High)
- CVE-2026-7916:Insufficient data validation in InterestGroups(High)
- CVE-2026-7917:Use after free in Fullscreen(High)
- CVE-2026-7918:Use after free in GPU(High)
- CVE-2026-7919:Use after free in Aura(High)
- CVE-2026-7920:Use after free in Skia(High)
- CVE-2026-7921:Use after free in Passwords(High)
- CVE-2026-7922:Use after free in ServiceWorker(High)
- CVE-2026-7923:Out of bounds write in Skia(High)
- CVE-2026-7924:Uninitialized Use in Dawn(High)
- CVE-2026-7925:Use after free in Chromoting(High)
- CVE-2026-7926:Use after free in PresentationAPI(High)
- CVE-2026-7927:Type Confusion in Runtime(High)
- CVE-2026-7928:Use after free in WebRTC(High)
- CVE-2026-7929:Use after free in MediaRecording(High)
- CVE-2026-7930:Insufficient validation of untrusted input in Cookies(Medium)
- CVE-2026-7932:Insufficient policy enforcement in Downloads(Medium)
- CVE-2026-7933:Out of bounds read in WebCodecs(Medium)
- CVE-2026-7934:Insufficient validation of untrusted input in Popup Blocker(Medium)
- CVE-2026-7935:Inappropriate implementation in Speech(Medium)
- CVE-2026-7936:Object lifecycle issue in V8(Medium)
- CVE-2026-7937:Insufficient policy enforcement in DevTools(Medium)
- CVE-2026-7938:Use after free in CSS(Medium)
- CVE-2026-7939:Inappropriate implementation in SanitizerAPI(Medium)
- CVE-2026-7940:Use after free in V8(Medium)
- CVE-2026-7942:Integer overflow in ANGLE(Medium)
- CVE-2026-7943:Insufficient validation of untrusted input in ANGLE(Medium)
- CVE-2026-7944:Insufficient validation of untrusted input in Persistent Cache(Medium)
- CVE-2026-7945:Insufficient validation of untrusted input in COOP(Medium)
- CVE-2026-7946:Insufficient policy enforcement in WebUI(Medium)
- CVE-2026-7947:Insufficient validation of untrusted input in Network(Medium)
- CVE-2026-7948:Race in Chromoting(Medium)
- CVE-2026-7949:Out of bounds read in Skia(Medium)
- CVE-2026-7950:Out of bounds read and write in GFX(Medium)
- CVE-2026-7951:Out of bounds write in WebRTC(Medium)
- CVE-2026-7952:Insufficient policy enforcement in Extensions(Medium)
- CVE-2026-7953:Insufficient validation of untrusted input in Omnibox(Medium)
- CVE-2026-7954:Race in Shared Storage(Medium)
- CVE-2026-7955:Uninitialized Use in GPU(Medium)
- CVE-2026-7956:Use after free in Navigation(Medium)
- CVE-2026-7957:Out of bounds write in Media(Medium)
- CVE-2026-7958:Inappropriate implementation in ServiceWorker(Medium)
- CVE-2026-7959:Inappropriate implementation in Navigation(Medium)
- CVE-2026-7960:Race in Speech(Medium)
- CVE-2026-7961:Insufficient validation of untrusted input in Permissions(Medium)
- CVE-2026-7962:Insufficient policy enforcement in DirectSockets(Medium)
- CVE-2026-7963:Inappropriate implementation in ServiceWorker(Medium)
- CVE-2026-7964:Insufficient validation of untrusted input in FileSystem(Medium)
- CVE-2026-7965:Insufficient validation of untrusted input in DevTools(Medium)
- CVE-2026-7966:Insufficient validation of untrusted input in SiteIsolation(Medium)
- CVE-2026-7967:Insufficient validation of untrusted input in Navigation(Medium)
- CVE-2026-7968:Insufficient validation of untrusted input in CORS(Medium)
- CVE-2026-7969:Integer overflow in Network(Medium)
- CVE-2026-7970:Use after free in TopChrome(Medium)
- CVE-2026-7971:Inappropriate implementation in ORB(Medium)
- CVE-2026-7972:Uninitialized Use in GPU(Medium)
- CVE-2026-7973:Integer overflow in Dawn(Medium)
- CVE-2026-7974:Use after free in Blink(Medium)
- CVE-2026-7975:Use after free in DevTools(Medium)
- CVE-2026-7976:Use after free in Views(Medium)
- CVE-2026-7977:Inappropriate implementation in Canvas(Medium)
- CVE-2026-7978:Inappropriate implementation in Companion(Medium)
- CVE-2026-7979:Inappropriate implementation in Media(Medium)
- CVE-2026-7980:Use after free in WebAudio(Medium)
- CVE-2026-7981:Out of bounds read in Codecs(Medium)
- CVE-2026-7982:Uninitialized Use in WebCodecs(Medium)
- CVE-2026-7983:Out of bounds read in Dawn(Medium)
- CVE-2026-7984:Use after free in ReadingMode(Medium)
- CVE-2026-7985:Use after free in GPU(Medium)
- CVE-2026-7986:Insufficient policy enforcement in Autofill(Medium)
- CVE-2026-7987:Use after free in WebRTC(Medium)
- CVE-2026-7988:Type Confusion in WebRTC(Medium)
- CVE-2026-7989:Insufficient data validation in DataTransfer(Medium)
- CVE-2026-7990:Insufficient validation of untrusted input in Updater(Medium)
- CVE-2026-7991:Use after free in UI(Medium)
- CVE-2026-7992:Insufficient validation of untrusted input in UI(Medium)
- CVE-2026-7994:Inappropriate implementation in Chromoting(Medium)
- CVE-2026-7995:Out of bounds read in AdFilter(Medium)
- CVE-2026-7996:Insufficient validation of untrusted input in SSL(Low)
- CVE-2026-7997:Insufficient validation of untrusted input in Updater(Low)
- CVE-2026-7998:Insufficient validation of untrusted input in Dialog(Low)
- CVE-2026-7999:Inappropriate implementation in V8(Low)
- CVE-2026-8000:Insufficient validation of untrusted input in ChromeDriver(Low)
- CVE-2026-8001:Use after free in Printing(Low)
- CVE-2026-8002:Use after free in Audio(Low)
- CVE-2026-8003:Insufficient validation of untrusted input in TabGroups(Low)
- CVE-2026-8004:Insufficient policy enforcement in DevTools(Low)
- CVE-2026-8005:Insufficient validation of untrusted input in Cast(Low)
- CVE-2026-8006:Insufficient policy enforcement in DevTools(Low)
- CVE-2026-8007:Insufficient validation of untrusted input in Cast(Low)
- CVE-2026-8008:Inappropriate implementation in DevTools(Low)
- CVE-2026-8009:Inappropriate implementation in Cast(Low)
- CVE-2026-8010:Insufficient validation of untrusted input in SiteIsolation(Low)
- CVE-2026-8011:Insufficient policy enforcement in Search(Low)
- CVE-2026-8012:Inappropriate implementation in MHTML(Low)
- CVE-2026-8013:Insufficient validation of untrusted input in FedCM(Low)
- CVE-2026-8014:Inappropriate implementation in Preload(Low)
- CVE-2026-8015:Inappropriate implementation in Media(Low)
- CVE-2026-8016:Use after free in WebRTC(Low)
- CVE-2026-8017:Side-channel information leakage in Media(Low)
- CVE-2026-8018:Insufficient policy enforcement in DevTools(Low)
- CVE-2026-8019:Insufficient policy enforcement in WebApp(Low)
- CVE-2026-8021:Script injection in UI(Low)
- CVE-2026-8022:Inappropriate implementation in MHTML(Low)
加えて、「Edge」固有の問題として以下の3件が修正されている。執筆時現在、まだ内容は公表されていない。
- CVE-2026-40416
- CVE-2026-41107
- CVE-2026-42838
デスクトップ版「Microsoft Edge」はWindows/Mac/Linuxに対応しており、現在公式サイトから無償でダウンロードできる。すでに「Microsoft Edge」を利用中の場合、待っていれば自動で更新されるが、手動での更新も可能。画面右上のメニュー([…]アイコン)から[ヘルプとフィードバック]-[Microsoft Edge について]画面(edge://settings/help)へアクセスするとよい。