ニュース
「Google Chrome 148」に79件の脆弱性、うち14件は深刻度最高の「Critical」
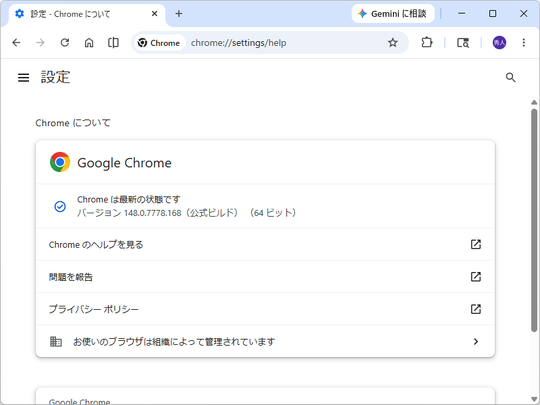
修正版がリリース、Windows環境にはv148.0.7778.167/168が展開中
2026年5月15日 13:03
米Googleは5月12日(現地時間)、デスクトップ向け「Google Chrome」の安定(Stable)チャネルをアップデートした。現在、Windows/Mac環境にv148.0.7778.167/168が、Linux環境にv148.0.7778.167が展開中だ。
本リリースは、79件の脆弱性を修正したセキュリティアップデート。CVE番号の付番は以下の通り。
- CVE-2026-8509:Heap buffer overflow in WebML(Critical)
- CVE-2026-8510:Integer overflow in Skia(Critical)
- CVE-2026-8511:Use after free in UI(Critical)
- CVE-2026-8512:Use after free in FileSystem(Critical)
- CVE-2026-8513:Use after free in Input(Critical)
- CVE-2026-8514:Use after free in Aura(Critical)
- CVE-2026-8515:Use after free in HID(Critical)
- CVE-2026-8516:Insufficient validation of untrusted input in DataTransfer(Critical)
- CVE-2026-8517:Object lifecycle issue in WebShare(Critical)
- CVE-2026-8518:Use after free in Blink(Critical)
- CVE-2026-8519:Integer overflow in ANGLE(Critical)
- CVE-2026-8520:Race in Payments(Critical)
- CVE-2026-8521:Use after free in Tab Groups(Critical)
- CVE-2026-8522:Use after free in Downloads(Critical)
- CVE-2026-8523:Use after free in Mojo(High)
- CVE-2026-8524:Out of bounds write in WebAudio(High)
- CVE-2026-8525:Heap buffer overflow in ANGLE(High)
- CVE-2026-8526:Out of bounds write in WebRTC(High)
- CVE-2026-8527:Insufficient validation of untrusted input in Downloads(High)
- CVE-2026-8528:Insufficient validation of untrusted input in SiteIsolation(High)
- CVE-2026-8529:Heap buffer overflow in Codecs(High)
- CVE-2026-8530:Use after free in Network(High)
- CVE-2026-8531:Heap buffer overflow in WebML(High)
- CVE-2026-8532:Integer overflow in XML(High)
- CVE-2026-8533:Use after free in Accessibility(High)
- CVE-2026-8534:Integer overflow in GPU(High)
- CVE-2026-8535:Out of bounds read in Media(High)
- CVE-2026-8536:Insufficient validation of untrusted input in ReadingMode(High)
- CVE-2026-8537:Insufficient policy enforcement in ViewTransitions(High)
- CVE-2026-8538:Insufficient validation of untrusted input in GPU(High)
- CVE-2026-8539:Script injection in SanitizerAPI(High)
- CVE-2026-8540:Type Confusion in V8(High)
- CVE-2026-8541:Out of bounds read in UI(High)
- CVE-2026-8542:Use after free in Core(High)
- CVE-2026-8543:Out of bounds read in FileSystem(High)
- CVE-2026-8544:Use after free in Media(High)
- CVE-2026-8545:Object corruption in Compositing(High)
- CVE-2026-8546:Out of bounds read in GPU(High)
- CVE-2026-8547:Insufficient policy enforcement in Passwords(High)
- CVE-2026-8548:Out of bounds write in Media(High)
- CVE-2026-8549:Use after free in Media(High)
- CVE-2026-8550:Use after free in Google Lens(High)
- CVE-2026-8551:Use after free in Downloads(High)
- CVE-2026-8552:Heap buffer overflow in GPU(High)
- CVE-2026-8553:Use after free in GPU(High)
- CVE-2026-8554:Type Confusion in ANGLE(High)
- CVE-2026-8555:Use after free in GTK(High)
- CVE-2026-8556:Inappropriate implementation in ANGLE(High)
- CVE-2026-8557:Use after free in Accessibility(High)
- CVE-2026-8558:Out of bounds write in Fonts(High)
- CVE-2026-8559:Integer overflow in Internationalization(High)
- CVE-2026-8560:Heap buffer overflow in SwiftShader(Medium)
- CVE-2026-8561:Incorrect security UI in Fullscreen(Medium)
- CVE-2026-8562:Side-channel information leakage in Navigation(Medium)
- CVE-2026-8563:Insufficient policy enforcement in IFrame Sandbox(Medium)
- CVE-2026-8564:Incorrect security UI in Downloads(Medium)
- CVE-2026-8565:Inappropriate implementation in Downloads(Medium)
- CVE-2026-8566:Insufficient policy enforcement in Payments(Medium)
- CVE-2026-8567:Integer overflow in ANGLE(Medium)
- CVE-2026-8568:Insufficient policy enforcement in AI(Medium)
- CVE-2026-8569:Out of bounds write in Codecs(Medium)
- CVE-2026-8570:Type Confusion in V8(Medium)
- CVE-2026-8571:Insufficient policy enforcement in GPU(Medium)
- CVE-2026-8572:Insufficient policy enforcement in Network(Medium)
- CVE-2026-8573:Integer overflow in Codecs(Medium)
- CVE-2026-8574:Use after free in Core(Medium)
- CVE-2026-8575:Use after free in UI(Medium)
- CVE-2026-8576:Inappropriate implementation in CORS(Medium)
- CVE-2026-8577:Integer overflow in Fonts(Medium)
- CVE-2026-8578:Out of bounds read in GPU(Medium)
- CVE-2026-8579:Insufficient validation of untrusted input in Skia(Medium)
- CVE-2026-8580:Use after free in Mojo(Medium)
- CVE-2026-8581:Use after free in GPU(Medium)
- CVE-2026-8582:Object lifecycle issue in Dawn(Medium)
- CVE-2026-8583:Insufficient policy enforcement in WebXR(Medium)
- CVE-2026-8584:Inappropriate implementation in Views(Medium)
- CVE-2026-8585:Inappropriate implementation in Media(Medium)
- CVE-2026-8586:Inappropriate implementation in Chromoting(Medium)
- CVE-2026-8587:Use after free in Extensions(Medium)
今のところ悪用の報告はないが、深刻度が4段階中最高の「Critical」と評価された脆弱性が14件も含まれており、できるだけ早いアップデートをお勧めする。
デスクトップ向け「Google Chrome」はWindows/Mac/Linuxに対応しており、現在、同社のWebサイトから無償でダウンロード可能。Windows版は、Windows 10/11に対応している。すでにインストールされている場合は自動で更新されるが、設定画面(chrome://settings/help)にアクセスすれば手動でアップデート可能。アップデートを完全に適用するには、「Google Chrome」の再起動が必要だ。